Pointers and Memory Management in Embedded C
Table Of Contents
Pointers and memory management are fundamental concepts in embedded C programming that directly impact the reliability, performance, and safety of embedded systems. Unlike desktop applications, embedded systems often operate with severe memory constraints, lack memory protection units, and require deterministic behavior. Mastering pointers and memory management techniques is therefore essential for developing robust embedded firmware.
Understanding Pointers in Embedded Context
In embedded C, pointers are variables that store memory addresses. They enable direct access to hardware registers, efficient data structure manipulation, and optimal use of limited RAM. However, improper pointer usage can lead to memory corruption, dangling pointers, and undefined behavior—issues that are particularly dangerous in safety-critical embedded applications.
Key considerations for pointers in embedded systems include:
- Memory-mapped I/O: Pointers are frequently used to access peripheral registers at specific memory addresses
- Function pointers: Essential for implementing callback mechanisms, state machines, and hardware abstraction layers
- Pointer arithmetic: Must be used cautiously to avoid accessing invalid memory regions
- Volatile qualifier: Critical when pointers refer to hardware registers that can change asynchronously
Memory Allocation Strategies
Embedded systems typically employ three primary memory allocation strategies, each with distinct trade-offs:
Static Memory Allocation
Memory is allocated at compile time. This approach offers:
- Deterministic behavior (no runtime allocation overhead)
- No fragmentation
- Predictable memory usage
- Limited flexibility (size must be known at compile time)
Stack Allocation
Automatic memory management for local variables and function calls:
- Fast allocation/deallocation
- Limited size (often constrained in embedded systems)
- Risk of stack overflow in deep recursion or large local variables
- Well-suited for temporary variables and function parameters
Dynamic Memory Allocation
Runtime memory allocation using malloc/free:
- Flexibility for variable-sized data structures
- Risk of heap fragmentation
- Unpredictable allocation time
- Potential for memory leaks and allocation failures
- Generally avoided in safety-critical embedded systems unless using specialized allocators
Best Practices for Safe Pointer Usage
To mitigate risks associated with pointers in embedded systems:
- Initialize Pointers: Always initialize pointers to NULL or a valid address
- Use Const Correctness: Apply const to pointers that should not modify data
- Limit Pointer Arithmetic: Prefer array indexing when possible for clarity
- Validate Pointers: Check for NULL before dereferencing in critical sections
- Use Volatile Judiciously: Apply to pointers accessing hardware registers or shared memory
- Avoid Casting Away Const/Volatile: This can lead to undefined behavior
- Prefer Static Allocation: When memory requirements are known at compile time
- Implement Memory Pools: For predictable dynamic allocation when needed
Common Pitfalls and How to Avoid Them
Dangling Pointers
Occur when pointers reference memory that has been deallocated or gone out of scope.
- Solution: Nullify pointers after freeing memory; avoid returning pointers to local variables
Memory Leaks
Result from allocated memory that is never freed.
- Solution: Implement strict allocation/deallocation pairing; use static analysis tools
Buffer Overflows
Writing beyond allocated memory boundaries.
- Solution: Use bounded string functions (strncpy, snprintf); validate indices
Misaligned Access
Accessing memory at addresses not aligned to data type boundaries.
- Solution: Use compiler-specific alignment attributes; pack structures carefully
Practical Examples
Memory-Mapped GPIO Access
#define GPIO_PORT_A_BASE 0x40004000#define GPIO_DATA_REG (*(volatile uint32_t*)(GPIO_PORT_A_BASE + 0x00))void configure_gpio_pin(void) {GPIO_DATA_REG |= (1 << 5); // Set pin 5 as output}
Function Pointer for Callback
typedef void (*callback_t)(uint8_t event);callback_t event_handler = NULL;void register_callback(callback_t cb) {event_handler = cb;}void handle_event(uint8_t event) {if (event_handler != NULL) {event_handler(event);}}
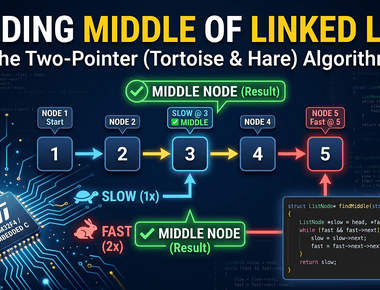
Static Linked List Node
typedef struct {int data;struct node* next;} node_t;// Static allocation of node poolstatic node_t node_pool[10];static int pool_index = 0;node_t* allocate_node(void) {if (pool_index < 10) {return &node_pool[pool_index++];}return NULL;}
Summary
Effective pointer and memory management in embedded C requires balancing flexibility with safety. Key takeaways include:
- Prefer static allocation when possible for determinism
- Use volatile correctly for hardware register access
- Initialize and validate pointers rigorously
- Understand the memory layout of your target microcontroller
- Apply const-correctness to prevent unintended modifications
- Consider memory pools for controlled dynamic allocation
- Utilize static analysis tools to detect pointer-related issues
By mastering these concepts, embedded engineers can create firmware that is not only functional but also robust, efficient, and safe—qualities that are paramount in the embedded systems domain.
Related Topics
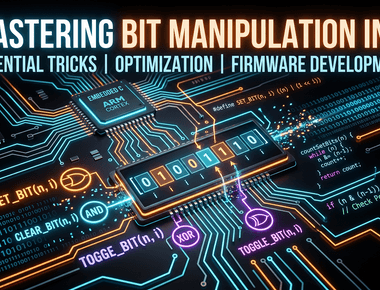
- Bit manipulation techniques for register-level programming
- Understanding the volatile keyword in embedded C
- Function pointers and callbacks in embedded systems
- Static vs dynamic memory allocation strategies
- Memory-mapped I/O fundamentals
Share
Related Posts



Quick Links
Legal Stuff